Every year, we get a few inquiries about why our web site doesn’t use https (i.e. TLS/SSL) to encrypt communications between the user and our site. Our stock answer has been that SSL is slow, expensive, and complicated for a two-person company to manage—and that was true for many years.
However, when I received the latest inquiry about encryption on the site, I thought it was time to revisit the subject. What I found is that SSL is no longer slow or expensive—and the complexity level has dropped dramatically. So we did a bit of work to update our pages, installed our shiny new security certificate, and as of now, you can securely browse Many Tricks by using this URL:
Note that we have not made this the default—but if you load the https site, you won’t be able to load the http version (thanks to something called HTTP Strict Transport Security).
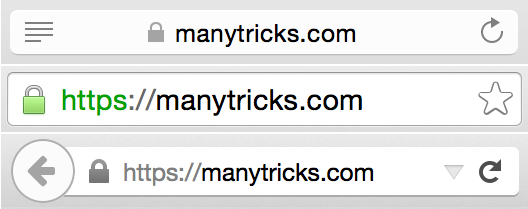
When you’re browsing our https site, you should see a small lock icon next to the site’s name, as seen below in Safari, Chrome, and Firefox:
We don’t collect any financial information here (all purchase details go through our processors, which have always used TLS/SSL encryption). But many people like the security of knowing that their interactions with a given site are encrypted. And now, they can be when you visit manytricks.com.
SHA-2 Hashes
The other thing we’ve done is create a page of SHA-2 hashes for all our apps. That page contains a list of SHA-2 hash values, and explains how to use these values to insure that what you download from us is the same as what we uploaded to the server. (Note that this is mostly useful for any potential download interceptions; if someone hacks our server such that they have full access, they could simply modify the SHA-2 values so that everything still looked right to a user.)
Please let us know if you have any troubles with either the https site (or our SHA-2 hash values)—we think we’ve tested everything, but it’s quite possible we’ve missed a page somewhere.
 Many Tricks
Many Tricks

You should make it the default; HSTS without redirecting everything from HTTP is a flawed implementation, incomplete. Not all browsers support it yet either, and those would need the redirect for any URLs you’ve sent out in the past.
In other words; don’t leave anything served over HTTP, redirect everything. That will also update your search results etc.
As for the hashes; use SHA256 or better, as SHA1 is already considered on its way out, getting close to possible collisions.
It will become the default soon, honest. Just working on a few more things on the back end.
-rob.
Hashes are now SHA-2; thanks for the pointer.
-rob.
Oh, and drop 3DES and CAMELLIA from your list of ciphers. Anything that still uses 3DES instead of AES ciphers doesn’t support SNI, which your site requires.
Quite honestly, I don’t have the slightest idea what you just said—I’ve never put together a list of ciphers. We’re using a third-party to provide and manage the certificate, so if this is something they generate, I have no control.
-rob.
I notice Moom and Leech 2 still check for software updates via manytricks.com on port 80 (not SSL/TLS port 443). It would be great if these communications channels were upgraded to https as well in the future :)
It’s great that you’re heading down this path of “encrypting all the things” as more people become concerned about the integrity of the software they run on their computers.
Good work guys!